Instances of fraud linked to domain names are an increasingly common threat to businesses. The ease of registration of domain names, accessible pricing, a lack of market knowledge of B2B actors, as well as other reasons make domain names seem like businesses’ digital Achilles heel. And with Cybersecurity Awareness month this month, it’s a subject that’s once again gaining attention.
How did domain names become targets for cybercriminals?
A domain name is a valuable article of intellectual property for your business. By definition, that which is valuable must also be difficult to access. The problem with domain names is that aquiring them is quite simple, both technically and financially, making them easy prey for cybercriminals.
Financially speaking, and despite the added value that can be accumulated on the domain name of a large brand over time, the price of registration remains stable and accessible (ranging between $15 and $100 on average per year). The cost to create a “counterfeit” domain name is, then, neglible compared to the profit that can be gained from its malicious use.
Technically speaking, the “first come, first served” rule applies to all domain name registration, making domains that the owners have fogotten to renew potentially strategic targets.
A growing threat regarding inventive new forms of domain name-related fraud
Over the last decade, instances of fraud linked to domain names have become a real problem for businesses. According to a study undertaken by WIPO (World Intellectual Property Organization), the number of suits related to domain names increased by 12% in 2018 alone.
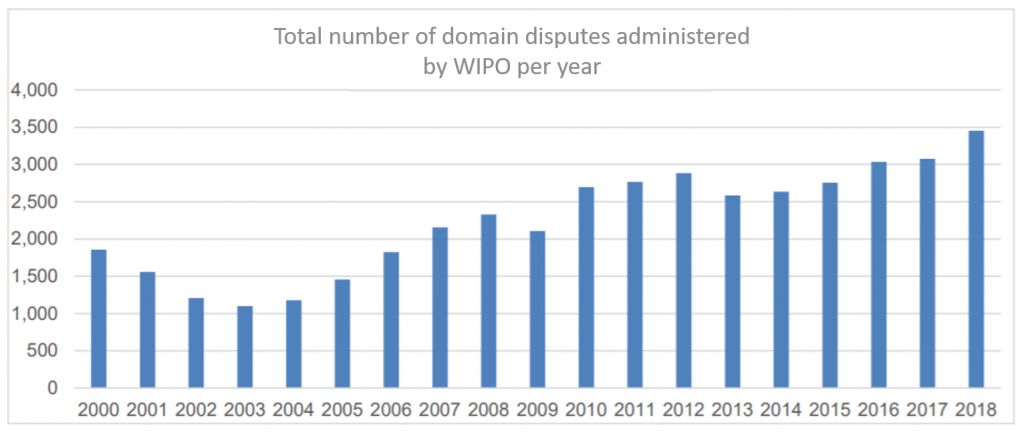
This troubling increase can be explained by three recent developments:
- The introduction of new TLDs starting in 2013 that have offered new opportunities to impersonate others’ brands,
- Increasingly regular promotional campaigns on certain TLDs that have provided greater accessibility to these TLDs,
- The implementation of GDPR since 2018, whose principle objective is to protect individuals’ personal data but can also contribute to indirectly sheltering malicious actors.
In the face of these new opportunities, fraudsters have been able to show a certain ingenuity in profiting from the popularity of brands. Here are the most common types of domain name abuse:
- Buying a domain name the owner has failed to renew in order to profit from a well-known brand
The simplest approach for cybercriminals is to bet on a lack of vigilance on the part of domain name owners. Forgetting to renew a domain name can result in it becoming available for any internet user to register. Certain companies have made this their business model, specializing in reselling sought-after domain names. It’s also very easy to prevent this by activating automatic renewal, an option offered by most professional domain registrars, including Gandi.
- Buyig a domain name with another TLD with the goal of causing damage to the brand
With more than 1,500 TLDs available, it’s very difficult for a business to protect its brandname and all its variants on all TLDs, which means further vulnerability. Anyone, then, can register a brand’s domain name on another TLD and profit from that brand’s reputation. This practice, which can be compared to a kind of parasitism, is the easiest and therefore more popular.
- Typosquatting
Changing just one character in a domain name is a particularly effective way of creating confusion. For example, ‘example.com’ might become ‘exarnple.com’ or ‘exampIe.com’. This strategy is best known as typosquatting and is hard to catch without relying on domain name protection pros.
- IDN homoglyph attack
Initially, only Latin characters were allowed in domain names. Since 2010, non-Latin characters have been progressively adopted, and today they are accepted by the majority of registries. We’re referring to IDN, or “Internationalized Domain Names.”
Similar to typosquatting, a homoglyph attack consists in taking advantage of the similarity between certain characters in non-Latin alphabets (the Cyrillic alphabet for example) to register domain names very close to and visibly indistinguishable from the domain name of a business being attacked. Taking our example of ‘example.com’ again, this might become ‘exɑmple.com’. The new and unconventional character of this type of attack makes it a formidable means of extracting profit from a brand’s popularity online.
- Adding a word in a domain name
In order to persuade internet users of the legitimacy of a domain name, cybercriminals also tend to register domain name adding a word letting them maintain an air of credibility. They might register ‘example-group.com’ or ‘example-us.com’ to take advantage of ‘example.com’. These variants are difficult to keep under control, given how varied they may be.
Whether this domain name abuse takes the form of phishing campaigns, selling counterfeit products, or other types of fraud, their impact on a business are necessarily negative:
- Loss of revenue related to an interruption of online services
- Loss of data, especially customer data
- Damage to your brand’s reputation
- Loss of trust on the part of internet users
That’s why it’s essential for every business to avail itself of brand protection services that are dedicated to detecting this type of malicious activity.
Brand protection services that prevent domain name fraud
Just like a business will opt for a professional phone subscription or internet connection, they should seek out the same level of service for domain names as well. Brand protection services have rapidly diversified over the last few years in order to offer effective defensive measures against domain name abuse.
By opting for a monitoring service, a business guarantees rapid reactivity in case of domain name fraud. A monitoring service will act as a kind of surveillance and detect illegitimate uses of domain names. Gandi’s monitoring service covers more than 1,200 TLDs, typographic variants, and even subdomains and IDN homoglyphs, sending alerts of any illegitimate domain name registration containing a brand name within 24 hours.
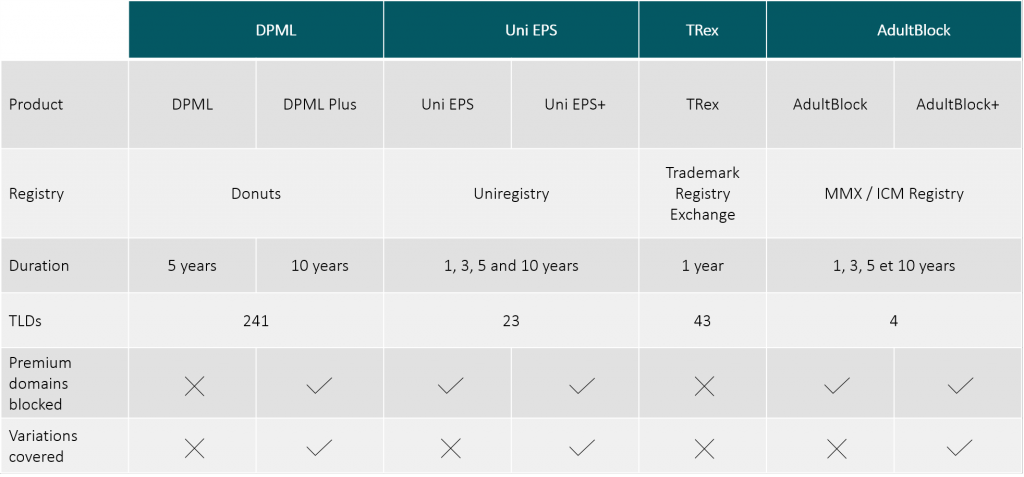
To go even further, a business can also use blocking services that have been implemented by various registries. DPML (Donuts,) Uni EPS (Uniregsitry), TRex (Trademark Registry Exchange) and AdultBlock (MMX/ICM Registry) let you block the registration of domain names on a wide variety of TLDs, and thereby stay in control of your online identity.
Finally, trusting in an expert to define your global, online, brand protection strategy lets you be sure that you’ve mastered your own online presence. An account manager can advise you on your domain name portfolio, helping you decide which purchases are most pertinent and ensuring daily management of your portfolio in order to guarantee its viability for the long run.
To learn more about domain name fraud and the solutions that exist to prevent it, feel free to contact your account manager or reach out to the Gandi Corporate Services team at corporatecontact@gandi.net.
Tagged in corporateSecurity